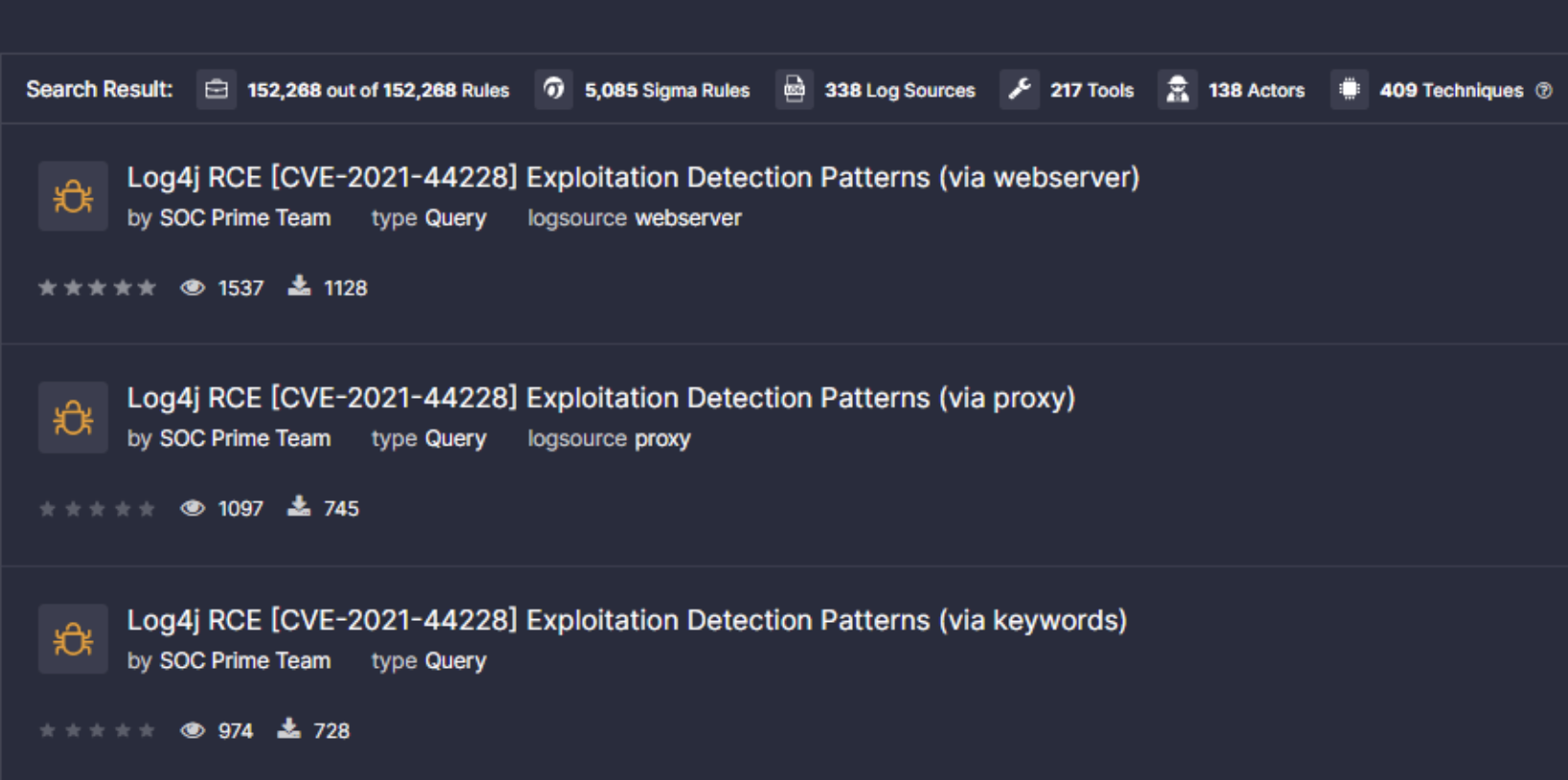
Detect exploits of Log4Shell, a critical RCE zero-day vulnerability in Apache Log4j first reported on November 24, 2021 and tracked as CVE-2021-44228:
- via web server logs
- via proxy logs
- via keywords in Linux logs.
SOC Prime highly recommends using Quick Hunt to make detection possible for each infosec or IT team.
Check out the SOC Prime Platform for new detections published.
Context of Log4Shell Vulnerability
Log4Shell, also known as LogJam, is an unauthenticated RCE vulnerability. Exploiting it, hackers can take possession of the complete control over the victimized system, which makes the potential impact truly disastrous.
The vulnerability (CVE-2021-44228) stems from flaws in the Apache Log4j Java-based logging library. The reported 0-day exists in the product versions 2.0-beta9 through 2.14.1 where the JNDI API has no protection against cases when endpoints are controlled by an adversary. With message lookup substitution enabled, threat actors can execute the malicious code having control over logged information or its parameters.
Log4Shell (CVE-2021-44228) is reported to be actively exploited in the wild. In fact, the cybersecurity community provides evidence that exploits can be dated back to March 2021.
Log4Shell Mitigation
To protect against possible attacks, companies can initiate the below-listed measures to mitigate the RCE in the Log4j flaw:
- Update to versions 2.15.0+ where the issues causing the vulnerability are resolved.
- In Log4j versions 2.10 through 2.14.1 you can set the system property "log4j2.formatMsgNoLookups" to “true”.
- In earlier versions, the issue can be resolved by removing the JndiLookup class from the classpath used by Java.
Since the list of affected products and components is being continuously updated, it's highly recommended to run Log4j detection to search for anomalies indicating that the system is compromised. The detections published on the SOC Prime Platform enable searching for suspicious activities related to possible exploitation of CVE-2021-44228.
Log4Shell Vulnerability Scope
Reasoning from the information published by numerous cyber security researchers, there is an active ongoing exploration for possible victims by threat actors.
The range of potential attacks seems to be extremely wide. The Log4j library, a project by the Apache Software Foundation, is used in a lot of systems and services. It's part of multiple Apache frameworks, such as Apache Struts2, Apache Solr, Apache Druid, and Apache Flink. This makes every system that uses them vulnerable. CVE-2021-44228 analysis shows that there are many popular systems that may be affected, including Steam and Apple iCloud.
Another alarming factor is the ease with which a Log4Shell exploit can be leveraged. Accordingly, a wave of attacks is expected. The PoCs of the exploit for Log4j Java libraries are already published online.
The vulnerability in Log4j was first reported to Apache by the Alibaba cloud security team in late November. Since then, more and more products have been found that are under threat.