In early September 2021, Microsoft published the warning of a zero-day flaw in MSHTML carrying identifier CVE-2021-40444 (severity rating 8.8/10). The Microsoft vulnerability is actively exploited to deliver Cobalt Stike Beacon loaders in targeted attacks as part of initial access tactics. The malicious campaigns typically originate from emails impersonating legitimate third parties like contractors or business partners. For a victim, it shouldn’t be a surprise to receive a Word or Excel file from such a sender and open to read it. However, once it happens, the remote code starts executing itself and swiftly deletes after the damage is done.
Below you will find more details on the CVE-2021-40444 exploit and discover appropriate detections. It’s worth noting that while a Microsoft vulnerability like this targets endpoint devices, it serves as just an entry point for further exploits. The strategic goal of attackers is to leverage a variety of tactics including credential theft and lateral movement to cause an organization-wide impact. That’s why early detection plays a major role in the mitigation of a more severe attack.
CVE-2021-40444 Vulnerability Context
The infected documents once downloaded, load an OLE Object HTML file that runs code with active JavaScript in one of the Internet Explorer’s native libraries - MSHTML. Consequently, this code creates a new ActiveX object which downloads a remote .cab archive with a DLL payload hidden in a file that normally is designed for describing the installation parameters of the object.
What makes this attack especially sophisticated is that the malicious payloads are programmed to hide within Windows in-built tools, acting like files that execute the normal system’s behavior. For example, they could target Alternate Data Streams (ADS) thus staying invisible for Windows UI. This technique might later be followed by path traversal with the help of CPL file payloads.
By mixing up the old and new techniques in multi-stage kill chains, attackers can use certain file types to download other encapsulated file formats, bypassing the traditional file transfer over the HTML protocol. This malicious code targets privileged accounts, that’s why users with administrative rights are more vulnerable to MSHTML Microsoft exploit than users with regular account configurations. It is important to deploy detection rules specifically for CVE-2021-40444 because otherwise, adversaries will be able to execute the exploit running undetected by common web proxies, Antivirus scans, and other security solutions.
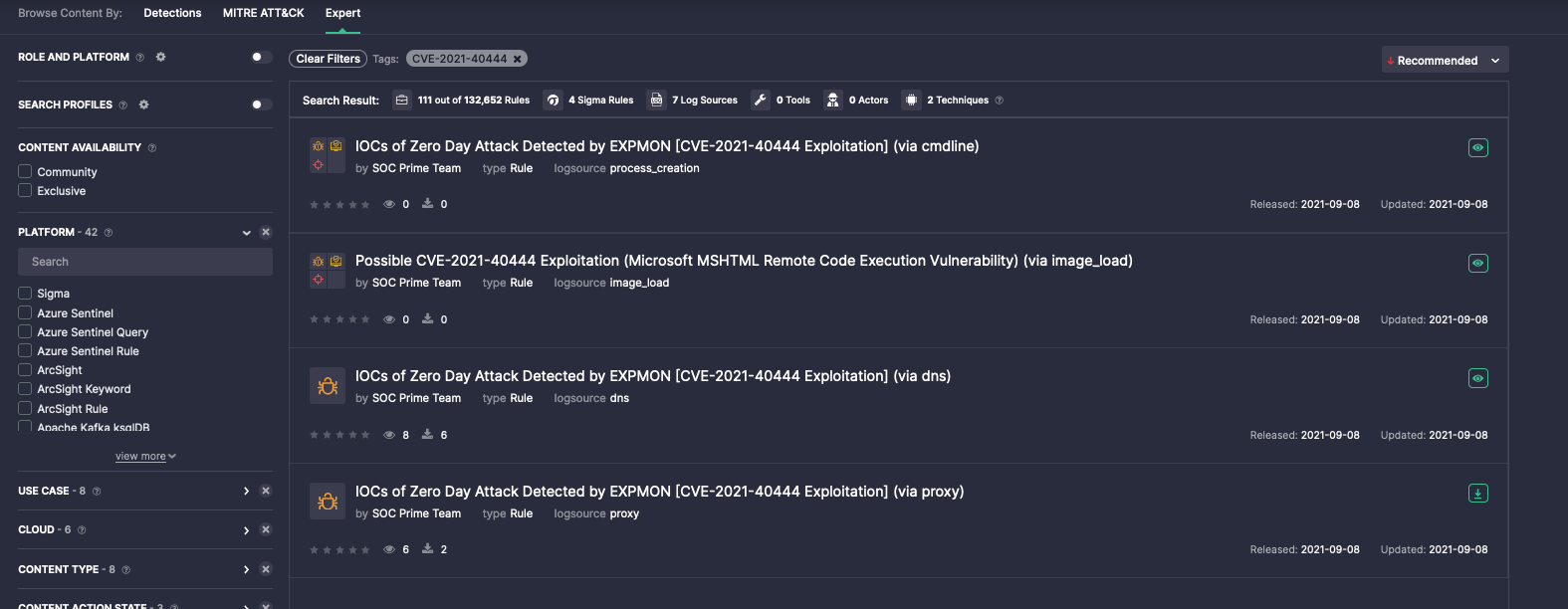
CVE-2021-40444 Detection
On our SOC Prime Detection as Code platform, you will find the particular IOCs for CVE-2021-40444 detection as well as behavior-based rules. Once you deploy these rules, you will be able to spot possible attack patterns.
Other important measures you can take to minimize the probability of CVE-2021-40444 exploitation:
- Enable attack surface reduction in Microsoft Defender for Endpoint.
- Disable ActiveX installation in Internet Explorer.
- Use the patches released by Microsoft.
Visit SOC Prime for accessing detection content items addressing the latest known vulnerabilities as well as zero-day attacks.