Password Security rule pack is the framework that finds passwords that are compromised by checking Microsoft Windows authentication logs for username field that could contain a user password. Use case includes a set of rules that make a search for passwords using regexp in username fields containing numbers, special characters, or other password required symbols. The result of rule trigger is a list of affected users and servers that are likely compromised.
Why passwords are compromised? When the user mistyped the password to the username field on the login form someone could see it, also all authentication failures are logged to Event Log that is not encrypted. Such logs are forward to SIEM system, log analytics will see the password as well. Thus, all accounts discovered by the use case must be investigated further and it is strongly recommended to change passwords.
Rule pack Dependencies & Recommendations
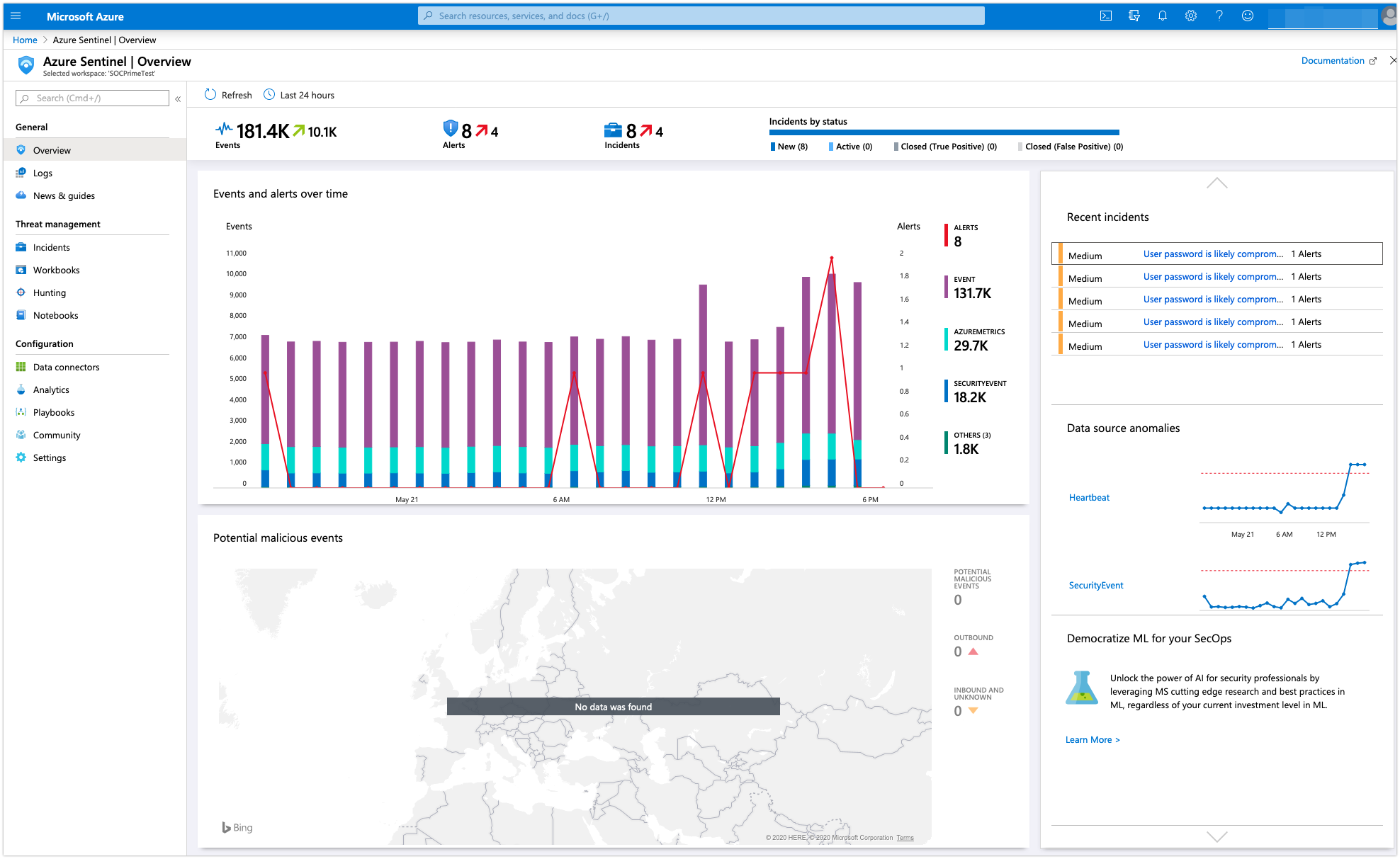
- Microsoft Sentinel
Rule Pack Log Source Requirements
- Microsoft Windows Active Directory and/or Workstations logs.