The SOC Prime Team released the Ransomware Detection pack of rules to help organizations withstand the latest ransomware attacks that are hitting major vendors around the globe. With a growing number of trends and more sophisticated intrusions, ransomware is considered to be the top challenge for most organizations in 2021, including large-scale enterprises.
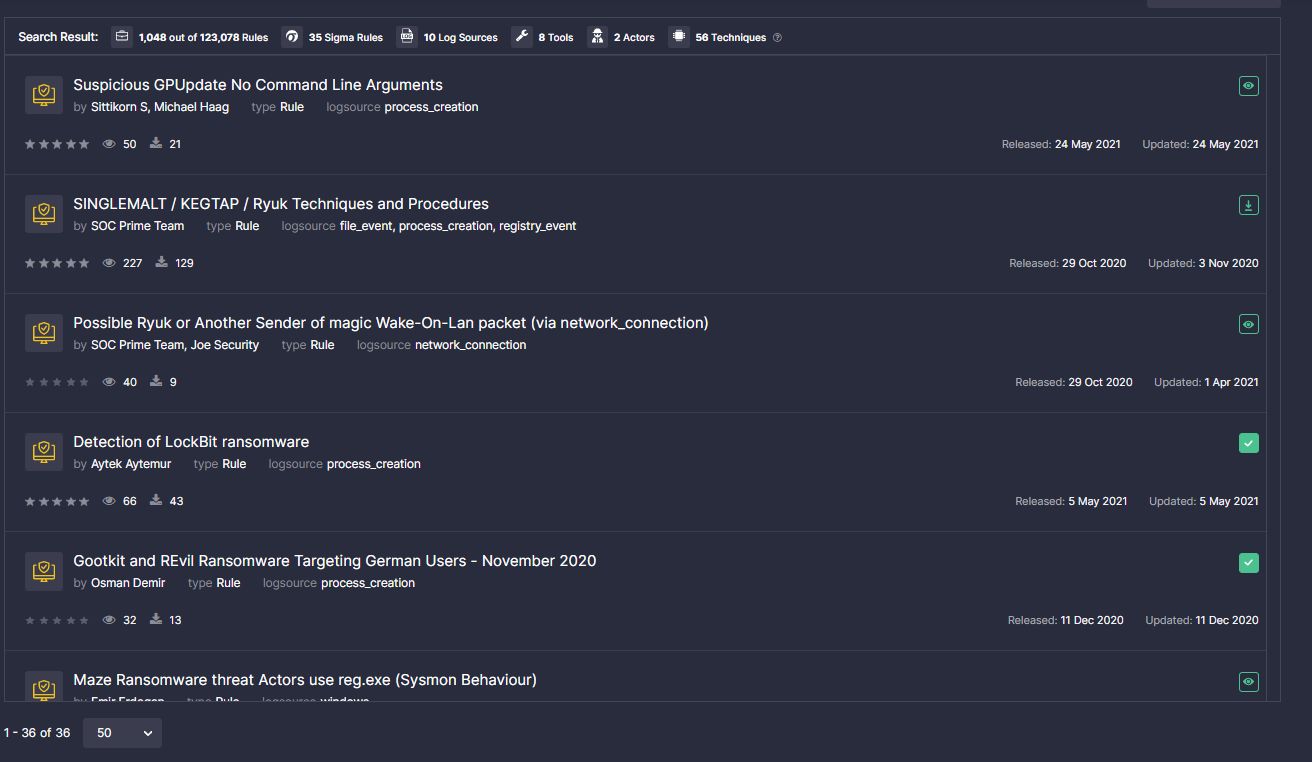
The set of rules involved in the Ransomware Detection Pack spots the malicious activity associated with the most nefarious ransomware samples in the arena, including Ryuk, DarkSide, DoppelPaymer, Conti, LockBit, Avaddon, and others. Detections for the devastating Kaseya supply chain attack by REvil gang are also on the list.
The dedicated Ransomware Detection Pack contains 35+ community rules mapped directly to the MITRE ATT&CK® framework v.9 and enriched with the corresponding references and descriptions.
To learn more about the threat landscape, have an overview of actors’ TTPs, and explore the best practices for ransomware defense, you can read our Industry Guidelines “Defending Against Ransomware Attacks in 2021.”